Trezor Login - Secure Access to Trezor Wallet
Introduction
Trezor Login provides users with a secure and seamless way to access their digital assets through the Trezor Wallet. As one of the most trusted hardware wallets in the crypto industry, Trezor ensures that private keys never leave the device, safeguarding funds from unauthorized access and online threats. With the growing popularity of cryptocurrencies, having a secure login method has become a necessity for investors worldwide.
Why Secure Login Matters
The cryptocurrency market operates 24/7, and with that comes the constant risk of hacking, phishing, and malware attacks. A secure Trezor login process ensures that users retain full control of their digital wealth without relying on centralized services. By combining offline storage with strong authentication methods, Trezor minimizes risks while giving users peace of mind.
Steps to Login with Trezor
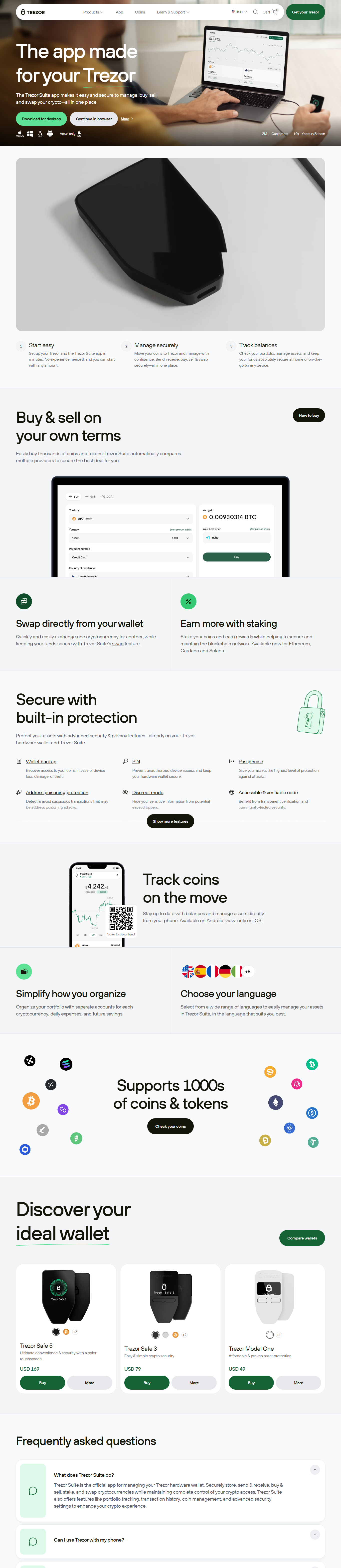
Logging into your Trezor Wallet is straightforward and designed to be user-friendly. Simply connect your Trezor device, open the Trezor Suite application, and follow the prompts. The device itself will display login requests, ensuring that sensitive information such as PINs and recovery seeds are never exposed online.
Step 1: Connect Your Device
Start by plugging your Trezor device into your computer or mobile device using the provided USB cable. The system will automatically detect the hardware.
Step 2: Open Trezor Suite
Download and install the Trezor Suite application from the official website. Once installed, launch the program to begin the login process.
Step 3: Enter PIN
The PIN pad is displayed securely on your device, not on the computer. Enter the PIN as instructed to prevent keyloggers or malware from intercepting your login credentials.
Step 4: Access Wallet
After authentication, you will gain access to your Trezor Wallet dashboard where you can manage, send, and receive cryptocurrencies.
Security Benefits of Trezor Login
The Trezor login process offers unmatched protection compared to conventional online wallets. By storing keys offline and requiring hardware confirmation for every action, hackers are unable to compromise user accounts remotely. Moreover, advanced features like Shamir Backup and passphrase support make it virtually impossible for unauthorized users to access funds.
Best Practices for Safe Login
To maximize the security of your Trezor login, always download software directly from official sources, avoid public Wi-Fi networks, and never share your recovery seed with anyone. Keeping your firmware updated ensures protection against newly discovered vulnerabilities.
Conclusion
Trezor Login is more than just a gateway to your wallet—it’s a shield protecting your digital future. With its combination of hardware security, encryption, and user-friendly design, Trezor sets the industry standard for secure crypto asset management. Whether you are a beginner or an experienced investor, logging in with Trezor ensures your funds remain safe from ever-evolving cyber threats.
In a world where digital security is becoming increasingly important, Trezor Wallet login gives you the confidence to explore, invest, and grow your crypto portfolio without fear. Protect your wealth the smart way—secure it with Trezor.